AWS Security Hub is a comprehensive security service provided by Amazon Web Services (AWS) that helps you centralise and automate security monitoring and compliance checks for your AWS resources.
But we won’t be able to monitor security hub on a daily basis or sometimes we can’t keep track of the vulnerabilities or when we create a new resource, we may forget to check if it is created without vulnerabilities.
So, today we are going to go through on how to setup alert if any vulnerability is found from security hub.
First we need to setup a SNS topic
Creating SNS topic
- Sign in to AWS Console.
- Open the SNS Console.
- Create a New SNS Topic.
- Configure Topic Details: You will be prompted to provide some details for your SNS topic:
- Name: Choose a name for your topic.
- Display Name: This is an optional field and can be used to provide a more descriptive name for your topic.
- Type: Standard
5. Press Create Topic.
6. Create a subscription
7. Protocol: Email
8. Endpoint: Your_email_ID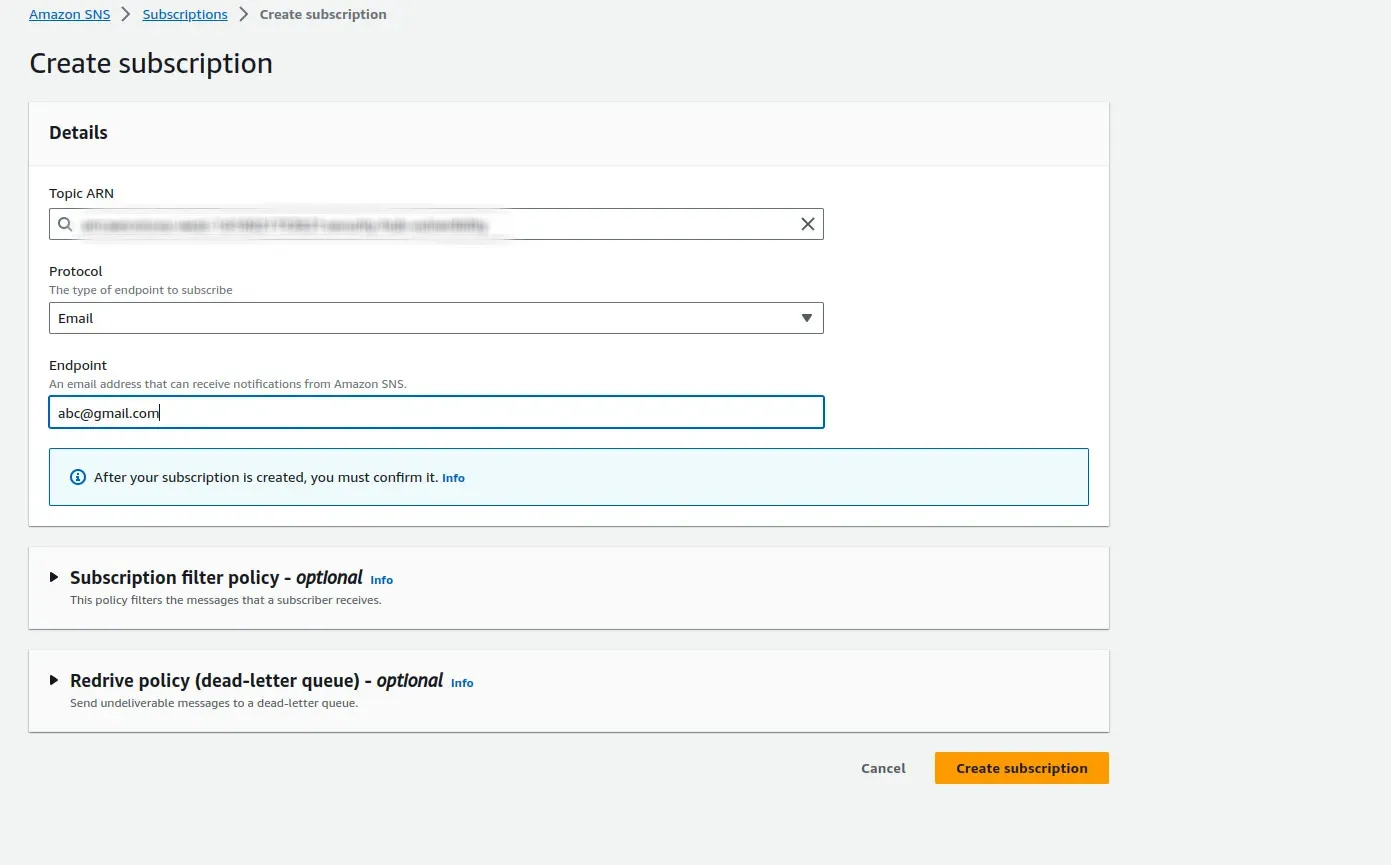
Creating EventBridge Rule
- Go to AWS Console
- Go to Eventbridge
- Go to rules in Eventbridge
- Click create Rule
- Give your rule a name and description(Optional)
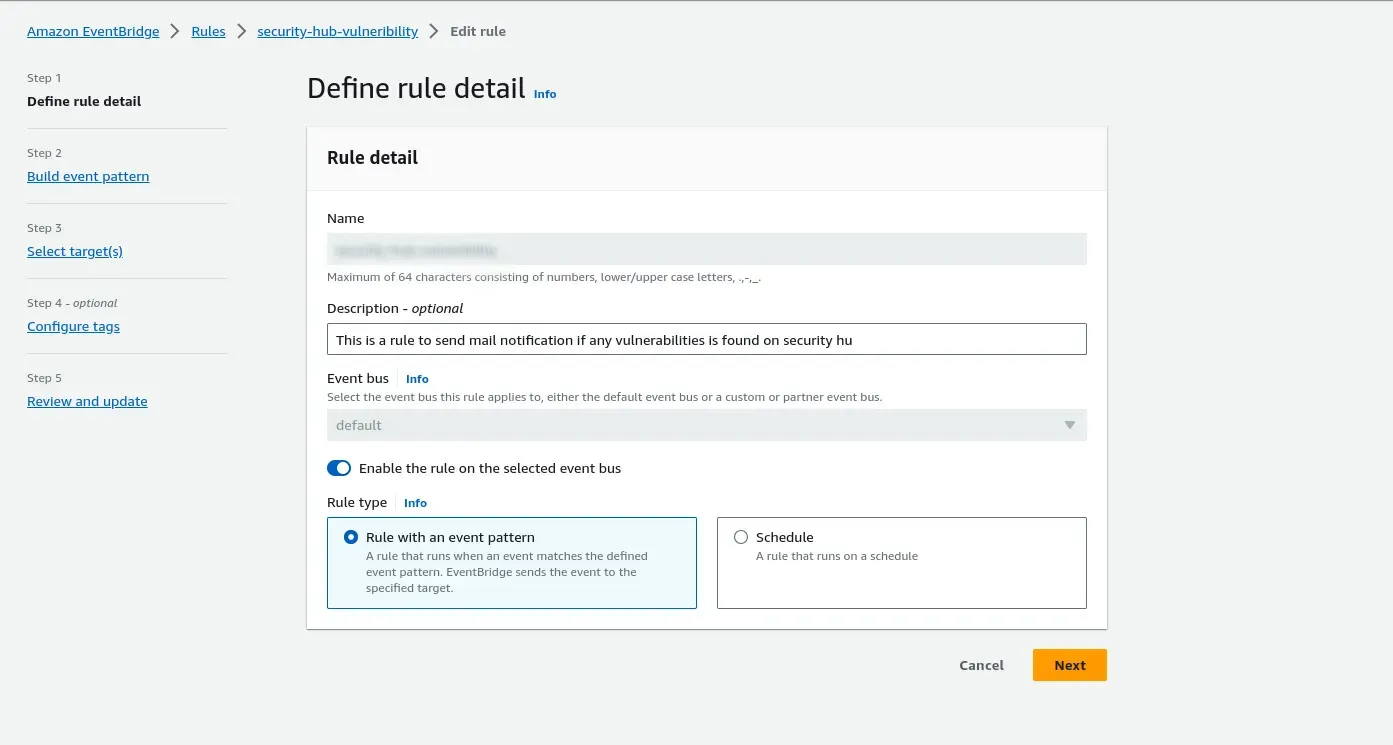
6. Click Next
7. Give AWS Events as Event Source
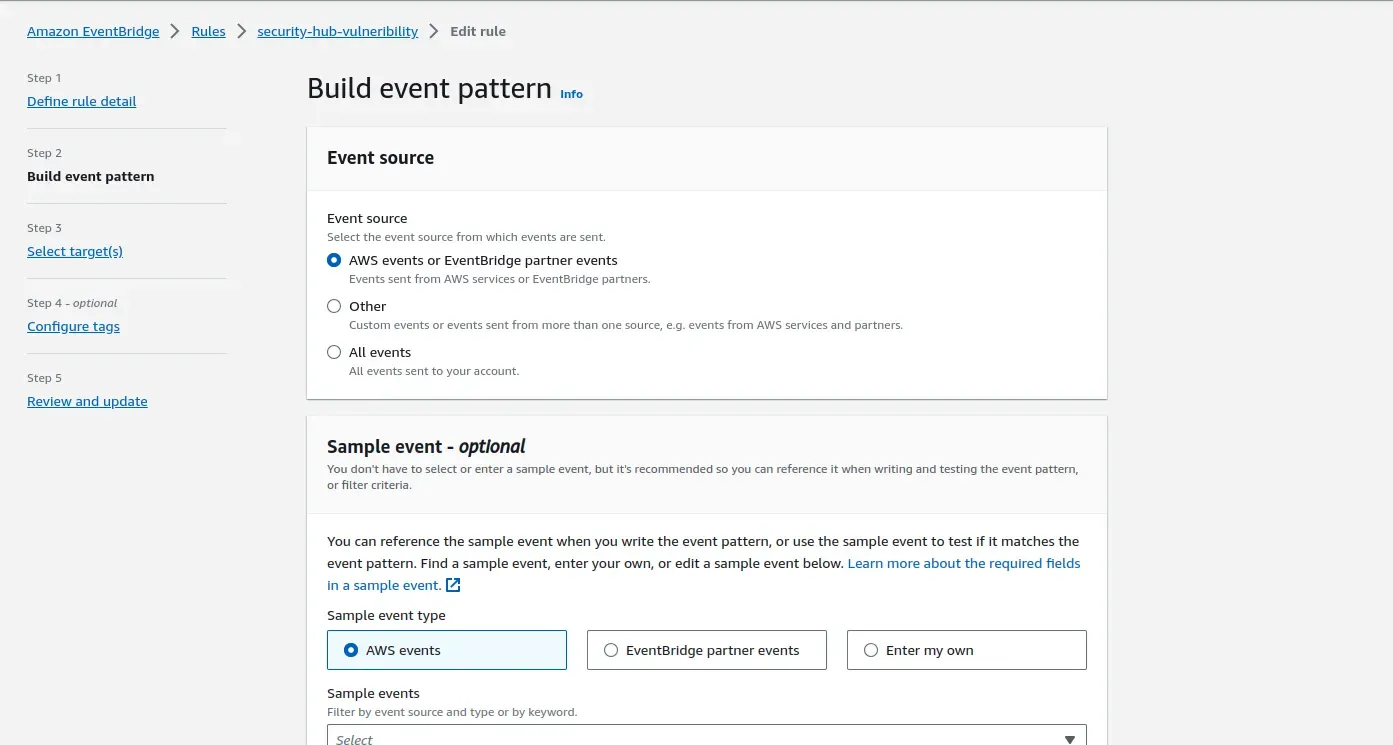
8. Go down to Event pattern
9. Event source: AWS Service
AWS Service: Security Hub
Event type: Security Findings - Imported
Specific compliance status: Failed
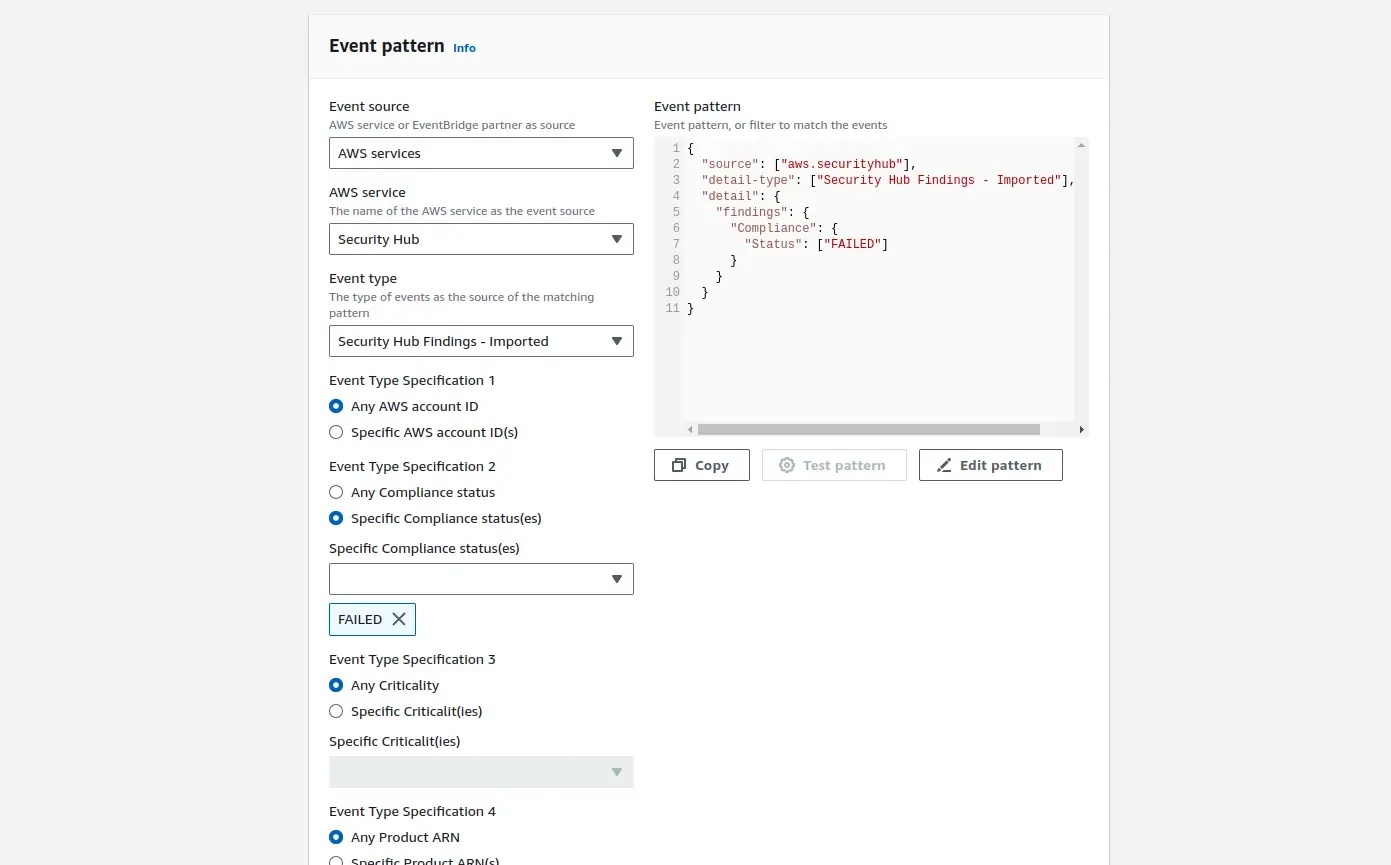
Example Json:
{
"source": ["aws.securityhub"],
"detail-type": ["Security Hub Findings - Imported"],
"detail": {
"findings": {
"Compliance": {
"Status": ["FAILED"]
}
}
}
}10. Click Next
11. We are going to use a lambda function to prettify our mail output, so we can choose the target as that lambda function or as we are going to set this eventbridge rule as the lambda’s trigger it will be updated as target automatically.
Creating a Lambda function
- Go to AWS Console
- Go to Lambda
- Create a new lambda function
- Give the lambda function an appropriate name and choose python 3.8 for now
- Copy the below python code
import json
import boto3
def send_sns_notification(message):
sns_topic_arn = "arn:of:your:sns:topic" # Replace with your SNS topic ARN
sns_client = boto3.client('sns')
response = sns_client.publish(
TopicArn=sns_topic_arn,
Message=message,
Subject="AWS Security Hub Finding Alert"
)
def lambda_handler(event, context):
try:
# Extract compliance status and finding ARN
findings = event['detail']['findings']
for finding in findings:
compliance_status = finding['Compliance']['Status']
finding_arn = finding['Id']
standard = finding['Compliance']['AssociatedStandards']
print(f"Compliance Status: {compliance_status}")
print(f"Finding ARN: {finding_arn}")
print(f"StandardID: {standard}")
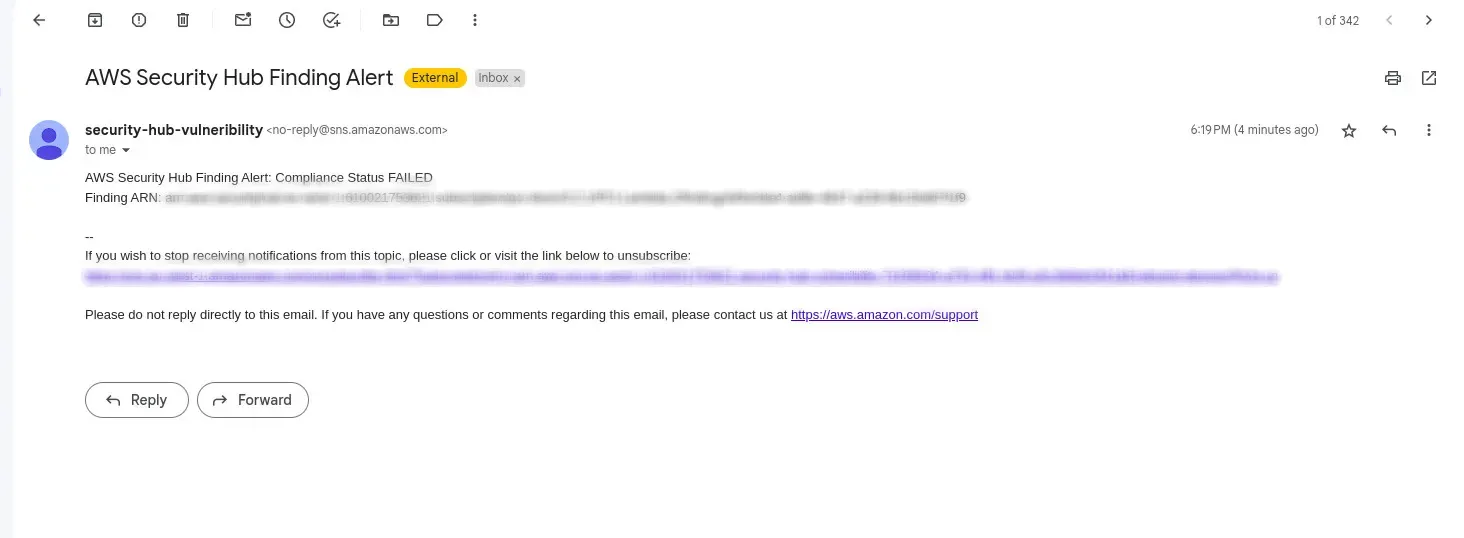
if compliance_status == "FAILED":
message = f"AWS Security Hub Finding Alert: Compliance Status FAILED\nFinding ARN: {finding_arn}\nStandardID: {standard}"
send_sns_notification(message)
return {
"statusCode": 200,
"body": json.dumps("Compliance status and finding ARN extracted successfully.")
}
except Exception as e:
print(f"Error: {str(e)}")
return {
"statusCode": 500,
"body": json.dumps("Error processing the event.")
}Note: You have to add “arn of your SNS Topic” in the code
6. As mentioned before choose the trigger of the lambda as the Eventbridge rule that we have previously created.
Wola! That’s it. You have created a vulnerability mail alert from Security Hub
Enhance your AWS security seamlessly! Automate vulnerability alerts through AWS Security Hub. Need assistance? Connect with SupportSages for expert guidance. Explore more about securing your AWS environment.
Click here to learn about AWS