Published on: October 29, 2019 by Nidhin George

Scenario:
A vulnerability (CVE-2019-11043) was identified which could affect websites running under nginx webserver with PHP-FPM enabled.
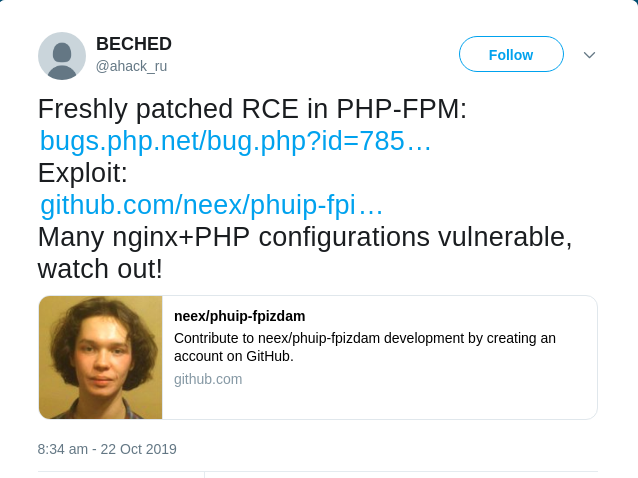
On October 22, a security researcher has tweeted regarding a freshly patched remote code execution vulnerability in PHP-FPM which exposed the bug .
You can find the GitHub repository which provides the proof of concept (PoC) for the vulnerability.
According to the PoC available in GitHub, a webserver running the below configuration is considered vulnerable.
location ~ [^/]\.php(/|$) {
...
fastcgi_split_path_info ^(.+?\.php)(/.*)$;
fastcgi_param PATH_INFO $fastcgi_path_info;
fastcgi_pass php:9000;
...
}
A website in considered vulnerable under the below conditions
Solutions:
To fix the vulnerability, PHP 7.3.11 and PHP 7.2.24 were released, the servers running nginx and PHP-FPM are advised to update the PHP versions to latest patched ones available.
Site owners who are unable to update the PHP running under the server can overcome the issue by adding a rule within the standard PHP mod_security firewall. You can find the instructions to do so here: https://lab.wallarm.com/php-remote-code-execution-0-day-discovered-in-real-world-ctf-exercise
Category : Linux, nginx, PHP, Vulnerabilities

Add new commentSIGN IN